vSphere 6.5 – Encrypted vMotion
Another good news is that You can encrypt the vMotion of any VM, encrypted or not – encrypted VM’s will always use encrypted vMotion :
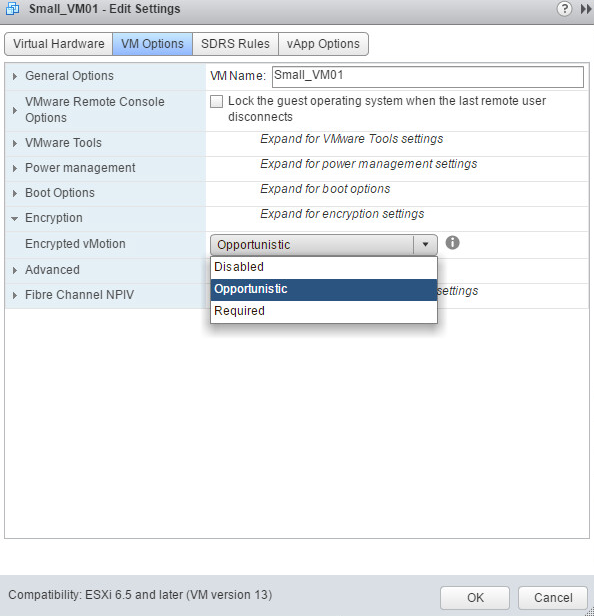
Disabled – do not use encrypted vMotion
Opportunistic – use encrypted vMotion if source and destination hosts support it.
Required -Allow only encrypted vMotion.
Note !!! Mixed cluster and you have a requirement of encrypted vMotion, then setting to “Required” will not let you vMotion to a host that doesn’t support it. (only vSphee ESXi 6.5 )
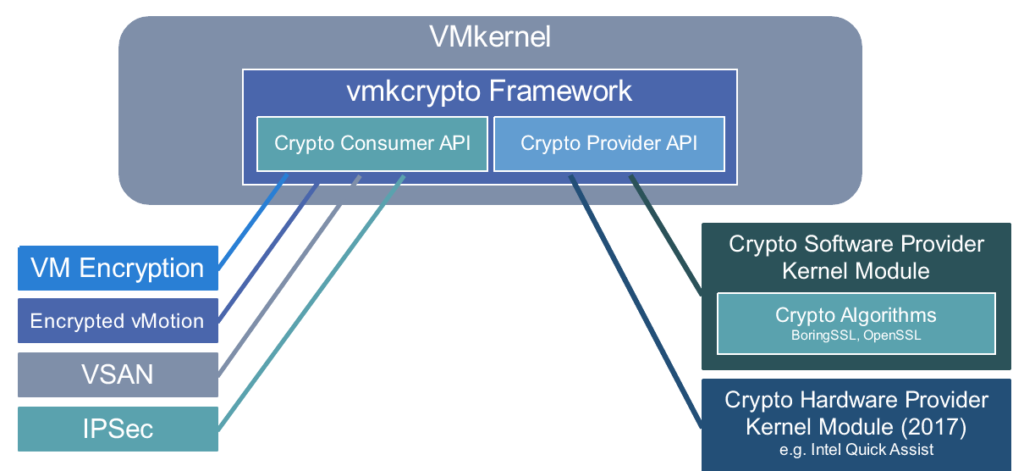
VMware add new vmkcypto framework subsystem to vmkernel. It is used by Virtual Mchine Encryption and vMotion for cryptographic operations :
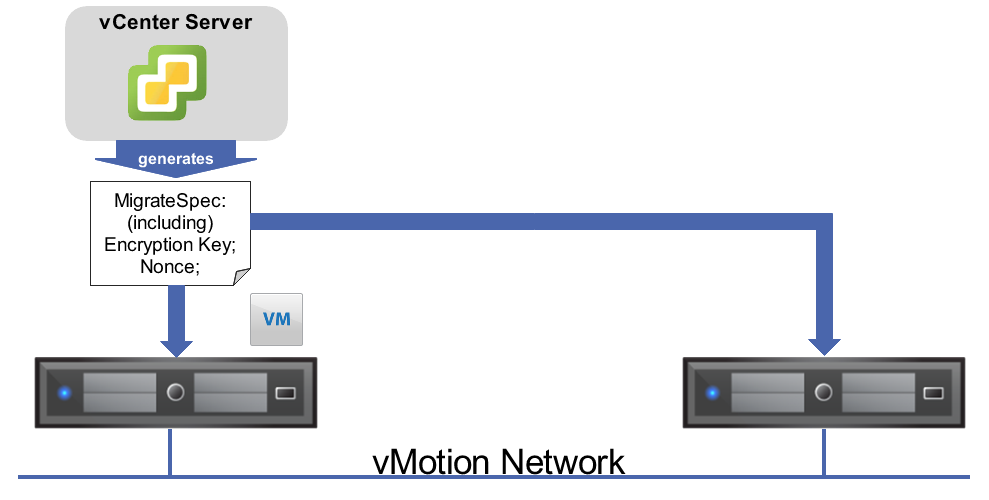
Now let’s look at new vMotion process:
- As part of that, a 256bit random key and 64-bit Nonce is generated. The Nonce used to generate a unique counter for every packet sent over the network. This prevents replay
- The key and the Nonce are packaged into a vMotion Migration Specification is created for the vMotion. This spec is sent to both systems in a the cluster.
- The vMotion traffic begins with every packet being encrypted on Host A and the counter incrementing.
- The packets are decrypted on the receiving host and the vMotion completes